Many computers are used for critical tasks or to process sensitive data. To protect a system, especially a portable system, that is running Windows, Microsoft has several security features in the latest Windows releases. Most people know about Microsoft Defender and biometric access, but in Windows 10 and Windows 11, there is also something called driver block rules.
Are Drivers Dangerous?
Device drivers are not dangerous per se. But device drivers, like many other critical components in the Windows operating system, run with a kernel-level execution priority. That means that even if drivers are not malicious, they can allow elevated control access.
Modern device drivers are all digitally signed, and often verified by Microsoft. And in the latest Windows versions unsigned drivers are not allowed to be installed unless special steps are taken to disable driver signature enforcement.
But even with a digital signature, there is no guarantee that the driver is completely safe. Digital signatures can be stolen (hacks of hardware/software companies, like Nvidia recently).
Recent malware attacks have leveraged the vulnerabilities of drivers to compromise system security. It makes a lot of sense to increase the protection of these system components.
What are Driver Block Rules?
Driver block rules are a set of rules that are recommended by Microsoft to block drivers that are malicious or not trusted. Drivers can be submitted to Microsoft for review and analysis and bad ones are added to the vulnerable driver blocklist. Hardware manufacturers and OEM partners will play a big role in keeping the rules actual and relevant.
How to use Driver Block Rules?
Microsoft is including a setting in the Windows Defender configuration to turn on this new feature called Microsoft Vulnerable Driver Blocklist. That means turning it on will activate the protection.
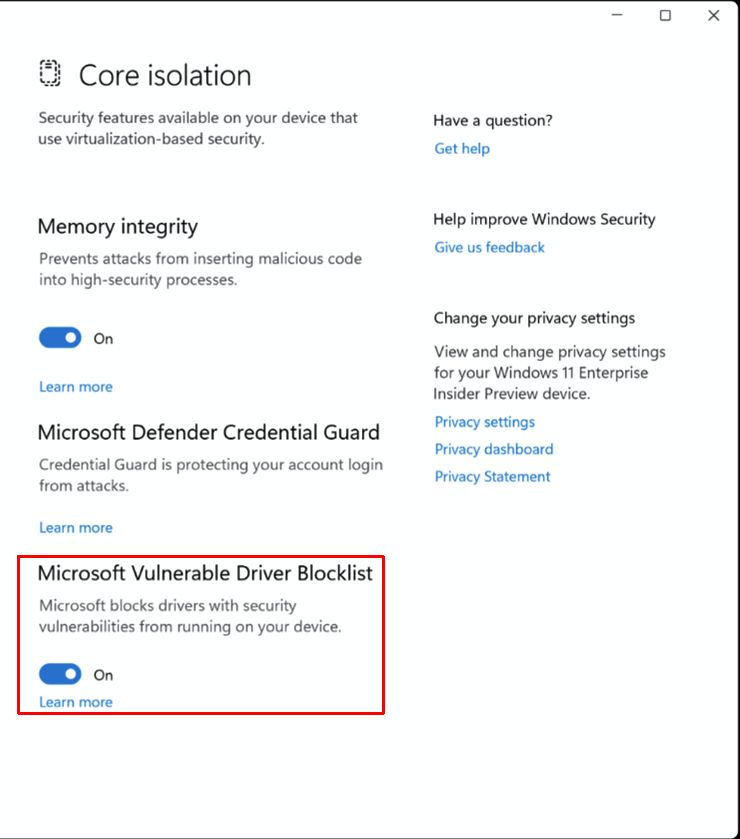
This new feature will be only activated by default on special Windows editions. Windows 10 S mode, and devices that have the Memory Code Integrity feature (or HyperVisor-protected Code Integrity – HVCI).
For Windows systems where the S mode or HVCI is not possible there is another option, which is using the Windows Defender Application Control (WDAC) policy. Details about how to use WDAC and the list of rules can be found on the Microsoft website.
WDAC is all about preventing apps or processes to run kernel level. Use and deployment of the rules is something that will typically be used by organizations with IT staff to implement this.
Driver BlockList Limitations
Although the concept the blocklist is good, the method strongly depends on the quality of the list. It was already found that the blocklist is not including all drivers that need to be blocked. Apparently new Windows versions were being issues a list from 2019! Microsoft already confirmed the issue and will address the problem in the Windows October updates to ensure the list is new and in sync across Windows 10 and Windows 11.
In addition, the block list is now on by default in Windows 11 (version 22H2). It also seems the option to disable the list is no longer present. Is Microsoft finally able to prevent the Blue Screens showing Stop errors caused by drivers?
For people still wanting to disable the list on Windows 11 version 22H2, there might be a workaround through the registry. But it is not an official and documented option.
Use the Registry Editor to find the folloing key:
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\CI\Config]
And create a DWORD Value in it named VulnerableDriverBlocklistEnable with a data value of zero (0).
- PCI Encryption/Decryption Controller Drivers for Windows 10 - February 16, 2025
- WD Passport Drives and How to Use Them with Windows 10: A Complete Guide - November 14, 2024
- How to Fix Unknown USB Device – Device Descriptor Request Failed - May 8, 2024

